Before you start using Windows PowerShell on an
Azure VM, you first need to ensure that Azure PowerShell module is installed on
the VM. Azure PowerShell module is the one which provided all the cmdlets to
manage the Azure VM infrastructure using PowerShell. You can download and
install the Azure PowerShell modules by running the Microsoft Web Platform
Installer on the VM. When prompted, click Run and the Web Platform Installer
will install the Azure PowerShell modules and all dependencies or you can visit
the link at http://azure.microsoft.com/en-us/downloads/#cmd-line-tools and
install the Azure command-line interface.
After the installation is complete,
you can verify whether the Azure module is available by using the Get-Module -ListAvailable command.
Before you start working with the cmdlets, you need
to authenticate to Windows Azure, you can either use the username and password
method or use a certificate to connect to the subscription.
The Windows Azure PowerShell module includes cmdlets
that help you download and import the certificate. First you have to use the Get-AzurePublishSettingsFile cmdlet which will
open the Azure Management portal for you to download the subscription settings
file. After downloading and saving the file to a location on the hard drive,
you can use the Import-AzurePublishSettingsFile
cmdlet to import the .publishsettings file for use by the module. This file
includes a management certificate that has security credentials.
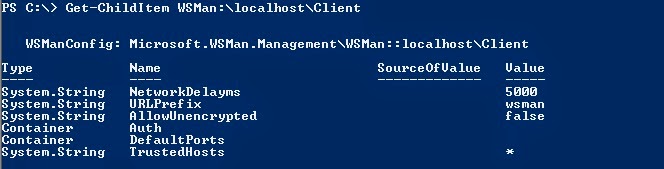
Once you have the subscription settings configured
properly, you can now use the remote commands as in any server. Remoting on Azure machine uses SSL and the
port 5986 by default. You can test this by trying to create a PowerShell
session like
Enter-PSSession azurevm1.cloudapp.net
–Port 5986 –UseSSL –Credential (Get-Credential)
If the certificate from the remote machine is not
added to the trusted authority of the local computer, then you’ll get an error
saying “The server certificate on the destination
computer (.cloudapp.net:) has the
following errors: The SSL certificate is signed by an unknown certificate
authority.” . If the certificate error is thrown then you need to add the
certificate from the remote server to the trusted authority.
If the common name of the certificate does not match
the hostname (server you are initiating the remote execution), you may need to
use the SkipCACheck and SkipCNCheck options while remoting.
Enter-PSSession -ComputerName
azurevm1.cloudapp.net -Credential (Get-Credential) -Port 5986 -UseSSL
-SessionOption (New-PSSessionOption -SkipCACheck -SkipCNCheck)